Other
.: 2017
by root on Jul.27, 2017, under Other
We haven’t died.. We’ve just been on life support for a while. We’re on the thaw and things will soon be at 98 degrees again.
Xenforo forums will be replacing the blog you have grown used to very soon.
ph33r.
.: bulk user deletion
by root on May.14, 2016, under Other
 My apologies to the few users who were legitimate – but I had 6000 users and I’m pretty sure about 2 or 3 were legit so I bulk deleted.. Please re-create your user and make sure you post at least one item so I can filter you out if this occurs again…
My apologies to the few users who were legitimate – but I had 6000 users and I’m pretty sure about 2 or 3 were legit so I bulk deleted.. Please re-create your user and make sure you post at least one item so I can filter you out if this occurs again…
.: when pigs fly…
by root on May.11, 2016, under Other
Things ha ppen in life. Mine has been a roller coaster of ups and downs and mostly self-inflicted damages that have often been difficult to recover from. Recover we do though (or we die – and that may happen later..) and this post is evidence of a bit of recovery.
ppen in life. Mine has been a roller coaster of ups and downs and mostly self-inflicted damages that have often been difficult to recover from. Recover we do though (or we die – and that may happen later..) and this post is evidence of a bit of recovery.
8bitunderground is once again back.. I have been collecting hardware again and have new plans for some of the plans I already had… Plans within plans as they say.
Not really sure I want to run any forums this time.. I think the niche of this blog is such that full blown forums will always be overkill. I will be a bit more chatty this time though and I’m not sure I want to litter the blog with random blabbering or not. So we shall see in the coming days/weeks if there is a go between that I could connect to the blog and allow for a bit more 2way discussion than the blog allows for now – and also without cluttering the important stuff.
That’s all for now – but not for long.
.: still here
by root on Feb.16, 2012, under Other
.COM Domain Name Renewal – 1 Year (recurring) $12.42
Quantity: 1 domain(s)
8BITUNDERGROUND.COM
Subtotal: $12.42
Shipping & Handling: $0.00
Tax: $0.00
Order Total $12.42
I will have some things to share shortly – as always life has gotten busy.. Hang in there if you are going through the same stresses I am. Hopefully it will get better, or maybe I will meet you at the ledge and we can talk each other down to have a beer?
.: spring is near
by root on Feb.27, 2011, under Other
 Tell me why I have to be a powerslave.
Tell me why I have to be a powerslave.
I really didn’t mean for the entire dead of winter to pass without making a post to this blog.
Really.
I apologize for 1/3 of the content here consisting of my apologies for a lack of posting. I have kept this domain for another year as I have every intention of continuing down the path of documenting the underground of yesterday but it seems like as I get older the more things that are trying to pull for equal access to my time.
Work and my side work has been claiming my time more than anything else. Stress has been fairly high lately and there have been a few other things going on as well. Additionally, I have decided that collecting 8bit gear isn’t really something conducive to me freeing up time and (more importantly) paying off my bills on the quest towards being debt free. With that said, I will be getting rid of most of what I have accumulated other than things that will likely be placed on display in my office such as my Apple Cat acoustic coupler, my Atari 830 Acoustic Coupler, my GameLine Modem, etc. Going on the block will be my prized C128-D, several commodore monitors, several C128’s, about 4 Atari 1050’s, an Atari 800xl that’s been modified with additional RAM, and the list goes on.
This is not to say that I won’t be looking out for special items, nor that I might not build a c128 or c64 hardware system again sometime, but I just haven’t really found anything that I can’t do within an emulator as it pertains to my endeavors of documenting the underground of the 70’s and 80’s.
I may also abandon my pet project of coding my own software database – which I did in Adobe Flex. Its not really the most flexible language despite its name, and the fact that it cant hook into MS Access, SQL, or any other true database natively is just kind of stupid. The way I am adding things to the database now is one of the reasons the project has stalled a little bit. The work flow is just slow and tedious.
Anyways. I will leave “all of you” with that to chew on as you wait for a real update from me, which I promise before summer. 🙂
One nice thing was that I did recently get a comment from a reader stating that he enjoyed the blog. I really appreciate that, and it was something that really made me want to continue on with this site.
See you soon.. Get your sunglasses ready! Spring is right around the corner.
.: merry Christmas 2010 / full circle.
by root on Dec.23, 2010, under Other
 So we sort of come full circle with this blog in a sense as I believe that it was Christmas of last year that I basically got it “started” even though I think we had a post or two prior to the Christmas 2009 post, it was really the one that got me feeling nostalgic and wanting to write about all of the things that I remembered from computing, phones, etc from my youth.
So we sort of come full circle with this blog in a sense as I believe that it was Christmas of last year that I basically got it “started” even though I think we had a post or two prior to the Christmas 2009 post, it was really the one that got me feeling nostalgic and wanting to write about all of the things that I remembered from computing, phones, etc from my youth.
So my image above that I believe comes from the Atari Historical Society (full credit due to them – great site!!!) because the 2600 was the first Atari hardware that entered my house, and really started my love affair with Atari that still exists today.
As I watch my nephew grow up, I am somewhat sad that he won’t have the same feelings to look back on that I have today – but maybe it is a blessing in disguise as those feelings are so intensely happy that they are also pretty sad in the fact that they are gone.
With that said – I am going to enter 2011 with resolve to continue the blog, and likely get the forums back up and running as well. So look forward to more rambling late night after maybe a few too many vodka tonics or whiskey’s on ice and pouring out of my blue heart to all 3 of my readers about how much I miss the old days as I allow the present to just slip by.
Yep, I’ll be one of those who will complain about how quickly life passed me because I sat around and dwelled about an 8 year period or so and the smell of styrofoam and silica gel packets that I can still smell in my nose as if I had just unwrapped them from under the tree.
Merry Christmas – 2010.
.: we’re still alive
by root on Sep.19, 2010, under Other
 just thought i would post a quick note that we are still alive and while I have closed the forums for now, the blog will remain open.
just thought i would post a quick note that we are still alive and while I have closed the forums for now, the blog will remain open.
through the nearly year long existence of this blog, i’ve only received one piece of correspondence indicating that people actually visit and enjoy this site, so it was somewhat easy to let summer fun get in the way of posting articles for a little while. i do still have an interest in sharing my love for old underground computing with others who might enjoy reading it though, so this site will remain.
for those of you who do visit and enjoy the site i want to say thank you very much for making this site part of your life.
.: archive updated!
by root on May.09, 2010, under Other
First of all I’d like to apologize for taking so long for the software review I promsied.. I look forward to doing it, but I had a wild hair to get some more stuff on the underground software archive and ended up adding about 16 new items to it. There are 15 new C64/128 hacking/phreaking apps added, and one Atari 2600 phreaking app added.
it, but I had a wild hair to get some more stuff on the underground software archive and ended up adding about 16 new items to it. There are 15 new C64/128 hacking/phreaking apps added, and one Atari 2600 phreaking app added.
I was also able to clean up some of the Adobe Flex code that I’ve been using for the software archive and in turn the code makes a little more sense to me now. There are several other things I will be doing such as adding lightbox to the blog, and if you haven’t noticed there is also a new “special projects” link at the top of the blog. The reason I added this section was that there were several things I wanted to cover that I thought were going to be much too extensive to dedicate just a blog post to. Things like the Atari Gameline Modem, Games Computers Play for the Atari 8Bit, Phone Man for the C64, and more. This will likely be a pretty exciting page to hit every week or two to see whats changed – though I’ll be posting updates on the blog and forums when something new hits as well.
With that said, the archive will continue to be updated – usually on the weekends, but potentially a new item or two during the week as well. The system for updating the archive isn’t as simple as just updating some HTML unfortunately, so I have to sit down and dedicate some time to it – which I usually have little of during the week.
As always – to the one or two of you that may be following this blog, thanks for the hits.
.: GameLine
by root on Mar.12, 2010, under Beginnings, Hardware, OldsCool, Telco
I’m back!
As is obvious from my blog, and the forums – I am a telecom/datacomm freak (phreak?) and developed quite an interest in modems at an early age.
Well – around 1980 or so I was thumbing through a gaming magazine and I stumbled across an advertisement about a device called the “GameLine” for the Atari 2600:
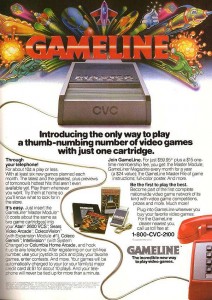 The gameline allowed you to plug a cartridge into your 2600, then plug a phone line into the cartridge (which obviously was also a modem) and then download games as well as do things such as primitive email, message boards, etc.
The gameline allowed you to plug a cartridge into your 2600, then plug a phone line into the cartridge (which obviously was also a modem) and then download games as well as do things such as primitive email, message boards, etc.
Well obviously when I saw this I was absolutely stunned, and begged my father for it for quite some time. Unfortunately dad knew that things like this would incur long distance charges, online time, membership fees, etc as he was already doing some timesharing type computer work for his employer. In short, I never got a GameLine – nor did I ever even see one in use.
Ebay has always sort of been a fountain of youth for me in that I have been able to buy some of the things that I was never able to have yesterday and play with them – or at least worship them – today.
I had watched the Ebay auctions for the GameLine unit for quite some time starting maybe 5 years ago, but the auctions were always ending with a bid much higher than I was willing to offer. About a month ago I saw one and just for fun bid $100 – about the most I would ever offer for something that I would never actually be able to use – and what do you know? I won the auction.
The box is in good condition, and the unit and all documentation – including a certificate for some free hours which looks like it was bundled with the unit as part of a local radio station contest – are in excellent condition.
I will be adding a page to this site to dedicate to the GameLine where I will post all images, links, and information about the device for any and all to peruse. I will also be dedicating a page to another somewhat similar service for the Atari 8-bit called “Games Computers Play”, or “GCP”.
I realize that the GameLine isnt an “underground” topic – but it is an item in the history of my life that certainly led to or at least added to my desire to get into telecomputing that led me into underground computing. Additionally its another one of those items that was only in production for a very short time and then was basically forgotten until people began archiving things on the Internet.
8 Bit Underground GameLine Page
8 Bit Underground Games Computers Play Page
.: Update
by root on Jan.12, 2010, under Other
 Check the forums tonight – I will be adding the first files to the download areas.. I very likely will NOT have time to add the app list to the blog tonight – but without a doubt *will* add some downloads to the forums.
Check the forums tonight – I will be adding the first files to the download areas.. I very likely will NOT have time to add the app list to the blog tonight – but without a doubt *will* add some downloads to the forums.
NOTE – The archive page is now live – albeit only with two entries. Please let me know if you have any issues. I will be updating the archive, blog, and forums quite a bit in the coming weeks/months. There is a GOB of material to sort through, screenshot, and document and I look forward to every bit of it!
I apologize for the delay and thank you very much for the hits here.
