Hardware
.: voice modems review: intro
by root on Feb.23, 2023, under Apps, Hardware, Other, Systems/Peripherals, Telco
In a bold, shocking new move b.8bu.com, we create a message post that does not conform to the typical text wrapping of the message around the image as every single other post has up until today. why? because I thought the header image so cool that I did not want to make it so small as to be unreadable. where did it come from you may ask – i will leave your googling skills to make that determination.
this post is simply being shown as an appetizer on an upcoming series i will be doing that discusses various devices and how they work as far as telephone number analysis (scanning, call progress detection, dtmf creation/generation, etc). most interesting to me at least is that the review will include several “telephony devices”, not just modems. i will use the first device reviewed to develop the framework for te others. hopefully real life stuff will allow me to do this before summer gets here.
as an added bonus i will be.doing these reviews using several methods of connectivity (magic jack, sip providere, aix providers, etc).
.: coming soon: the charlie board.
by root on Nov.29, 2018, under Hardware, OldsCool, Telco
Leave a Comment more....: GameLine
by root on Mar.12, 2010, under Beginnings, Hardware, OldsCool, Telco
I’m back!
As is obvious from my blog, and the forums – I am a telecom/datacomm freak (phreak?) and developed quite an interest in modems at an early age.
Well – around 1980 or so I was thumbing through a gaming magazine and I stumbled across an advertisement about a device called the “GameLine” for the Atari 2600:
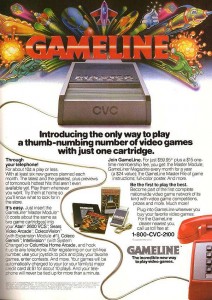 The gameline allowed you to plug a cartridge into your 2600, then plug a phone line into the cartridge (which obviously was also a modem) and then download games as well as do things such as primitive email, message boards, etc.
The gameline allowed you to plug a cartridge into your 2600, then plug a phone line into the cartridge (which obviously was also a modem) and then download games as well as do things such as primitive email, message boards, etc.
Well obviously when I saw this I was absolutely stunned, and begged my father for it for quite some time. Unfortunately dad knew that things like this would incur long distance charges, online time, membership fees, etc as he was already doing some timesharing type computer work for his employer. In short, I never got a GameLine – nor did I ever even see one in use.
Ebay has always sort of been a fountain of youth for me in that I have been able to buy some of the things that I was never able to have yesterday and play with them – or at least worship them – today.
I had watched the Ebay auctions for the GameLine unit for quite some time starting maybe 5 years ago, but the auctions were always ending with a bid much higher than I was willing to offer. About a month ago I saw one and just for fun bid $100 – about the most I would ever offer for something that I would never actually be able to use – and what do you know? I won the auction.
The box is in good condition, and the unit and all documentation – including a certificate for some free hours which looks like it was bundled with the unit as part of a local radio station contest – are in excellent condition.
I will be adding a page to this site to dedicate to the GameLine where I will post all images, links, and information about the device for any and all to peruse. I will also be dedicating a page to another somewhat similar service for the Atari 8-bit called “Games Computers Play”, or “GCP”.
I realize that the GameLine isnt an “underground” topic – but it is an item in the history of my life that certainly led to or at least added to my desire to get into telecomputing that led me into underground computing. Additionally its another one of those items that was only in production for a very short time and then was basically forgotten until people began archiving things on the Internet.
8 Bit Underground GameLine Page
8 Bit Underground Games Computers Play Page
.: iWoz
by root on Feb.15, 2010, under Hardware, Non-Fiction, OldsCool
Well so it’s pretty much the same as anything that I get involved and interested over – life gets in the way and things get placed on the back burner to cool. Yet while the pot was sitting there congealing, 8 Bit Underground was on my mind the entire time  as I worked on this and that which was required of “the real world” for the past week or two.
as I worked on this and that which was required of “the real world” for the past week or two.
Now then – on to something relevant.
I read quite a bit. About 10 percent of the books I read I enjoy, and about 1 percent I would recommend to someone else. iWoz by Steven Wozniak is one of those books that falls into the 1% category, and initially I thought it was going to fall into that 90% category of which I don’t like.
Wozniak obviously wrote most of the book, or – his editor totally sucks. The prose is rough, and the writing mistakes for a book that were made are probably trumped only by the mistakes that you might find in this blog. 🙂
But those things aside, it was Wozniak’s somewhat self righteousness that I didn’t like. He is pompous and full of himself, and that draws out very well in the text. As I read on though, I began thinking about who this person is that I am reading about. This is Steve Wozniak – co founder of Apple and the engineering genius behind a machine that pretty much set the stage for everything that I love – and everything that this blog is about.
To add a little sauce, we have an entire chapter – really a little more than a chapter – dedicated solely to phreaking. Most of it is about Woz and Jobs blue boxing exploits, but there are some other morsels there as well.
I am about halfway through with the book now and I am just getting to the part where Jobs is working at Atari under the Bushnell regime and Wozniak is being asked to come down and code Breakout. By this point I am taking the book, and the man – for what they are and I am enjoying the thing.
If anyone would like the book, drop me a private message on the forums (or here) and I will be happy to send it to you when I’m done with it – free.
I will not plug many things here – and certainly not many “modern day” things – but I think the book is a good read for most of the audience that visits this site. Pick it up – or be the first to tell me you want it.
.: beginnings (part one) :.
by root on Nov.23, 2009, under Beginnings, Hardware, OldsCool, Systems/Peripherals
And so here we are again, another week and another post.
My intention is not to limit posts to once a week, or to promise more than one post a week. What I do hope to provide is at the very least one new post a week with hopefully more. With that said, we have some time to spend here and even though this blog (and the forums) will mostly be about underground related items, I feel like there needs to be some introductory things covered just so you’ll have an idea of who I am and where I came from as far as technology goes.
No, I am not going to list every game system I ever played or every hacker book that I read – but I do feel like there are a few stepping stones to cover that will transport us into the shadowy world that we will be focusing on here.
And with that said, “beginnings (part one)” deals with a device that became very popular in the mid 70’s and lasted through various iterations into the mid 80’s.
The TI Silent 700.

My first experience with this device was when my father brought one home from where he worked at a large military subcontractor. Turns out there was some work that could be done from home for fairly decent money doing data entry on these things.
My parents never discouraged me from technology – but I remember as the 700 sat underneath the telephone in our kitchen on a typewriter table and my father tried time and time again to get the stupid thing to connect to the mainframe on the other end I was shooed away from the scene several times. In hindsight it was all deserved – I was somewhat of a mischief maker and I was always getting into things I shouldn’t be. So it should have been no surprise that my parents would have wanted to keep me from messing with or becoming interested in this surely expensive device.
So I sat in the den on the couch listening to the handshake tone and my fathers cries of obscenity over his inability to get the 300 baud connection that he so desperately wanted so that my mom could make some side coin doing data entry.
It wasn’t until everyone had gone to bed that evening that I found the piece of paper with the phone number, login and password to the mainframe that my dad had been trying to connect to – and with the air conditioner,  fridge, TV, and my parents chattering now absent, I connected to the remote machine on the first try.
fridge, TV, and my parents chattering now absent, I connected to the remote machine on the first try.
I had entered the login and then the password and had just been presented with a very minimal “main menu” when my father crashed in hanging up the off yellow GTE handset onto the rotary base that hung on our wall via some crazy ITT adapter and scurried me off to my bedroom – the silent 700 taken back to work never to return.
It had all happened really in the course of 5 minutes – or if you want to include the time I watched as my parents attempted to get connected – maybe 2 hours and 5 minutes.
One thing was for certain though – I was absolutely dumbfounded over the fact that some how our telephone was able to ask for and capture a username and something so very “spy like” called a *password* and then provide me with a menu of things I could do with that machine I had just connected to.
Months would go by where I would lie in bed looking up at the square smoked light fixture in the dark as I waited for sleep wondering what kind of wonderous things I might have been able to do had I been able to have spent more time with that machine.
more time with that machine.
Even more, I had the imagination to think that there might be tons of phone numbers that answered with that funny tone and if I had one of those suitcase based machines I could talk to all of them.
This was probably around 1977 or so. A time in which I had not really been exposed to anything more than “pong” and a little bit exposed to the video gaming craze that was beginning to overtake the malls that I would go to. It was a time that I was still dreaming of becoming an astronaut, a police officer, or a professional football player while at the same time touring the world as the new guitarist of KISS.
At this point computer people were those people who ran around with pocket protectors with greasy hair and funny glasses – tinkering with blinking lights and huge buttons and twirling tape drives all mounted in a blue steel cabinet in some mountain somewhere. A place where tractor fed green and white striped paper was everywhere and people who actually touched the computer had to wear clean suits.
But it was a start – and from what I remember, it was the beginning.
This is not your son’s Internet.
This is The 8 Bit Underground.